How Does Bitcoin Record Transactions?
From signed transactions to blocks to the blockchain. How Bitcoin creates a tamper-evident record of every transfer ever made.

Introduction
In the previous article, I explained the cryptographic concepts that Bitcoin builds on: hash functions provide integrity, and key pairs provide authenticity through digital signatures. But how does Bitcoin actually apply these concepts?
In this article, I will answer that question in three steps. First, I will explain what a transaction is and how it is secured. Then, I will show how transactions are grouped into blocks. And finally, I will explain how blocks are linked together to form the blockchain.
What Is a Transaction?
In everyday language, a transaction is simply a transfer of value. In Bitcoin, the meaning is more specific. Andreas M. Antonopoulos defines it in his book "Mastering Bitcoin" as follows:
"In simple terms, a transaction tells the network that the owner of certain bitcoins has authorized the transfer of that value to another owner." — Mastering Bitcoin: Programming the Open Blockchain (O'Reilly Media, 2023)
Here is an example. Alice owns two bitcoin. She wants to send one bitcoin to Bob. Before she can do that, she needs Bob's address. Every Bitcoin user has an address, which is derived from their public key through hashing. It is what you share with others to receive bitcoin.
Alice creates a transaction that states: "I, Alice, authorize the transfer of one bitcoin to Bob's address." But before she can send this transaction to the network, she needs to prove that she is authorized to send this bitcoin. How does she do that?
How a Transaction Is Secured
Remember the king's seal from the last article? Signing a transaction works the same way. Alice presses her private key into the transaction, creating a seal that anyone can inspect but no one can forge. Let's walk through the process.
Signing
Alice has her transaction ready. Now she secures it in two steps.
First, she passes the transaction through a hash function. This produces a fixed-size fingerprint of the transaction, exactly as we have seen before. Any change to the transaction, no matter how small, would produce a completely different fingerprint.
Then, she takes this fingerprint and her private key and passes both to a signing function. The result is a digital signature: cryptographic evidence that Alice, and only Alice, authorized this specific transaction, because only she is the owner of this specific private key.
Alice sends the transaction to the network, along with this signature and her public key.
Verification
When a computer in the network receives the transaction, it needs to verify several things: Does the transaction conform to the rules of the protocol? Is the signature valid? Does Alice actually have the bitcoin she wants to send? And has she already spent the same bitcoin in another transaction?
The computer checks each of these. Let's focus on what the signature alone proves. The computer passes the transaction through the same hash function Alice used. This produces a new fingerprint. Then, the computer takes this fingerprint, the signature it received, and Alice's public key, and passes all three to a verification function. The function returns either true or false.
If the result is true, the computer knows the following:
Authenticity: The signature proves that only the owner of the corresponding private key could have signed this transaction. Therefore, the transaction is genuinely from Alice.
Integrity: As we have seen, even the smallest change to data produces a completely different hash. If anyone had modified the transaction during transmission, the fingerprint would not match, and the signature would be invalid.
Non-repudiation: This follows from the first two. Alice cannot deny having signed this transaction. Since only her private key could have produced this signature, the evidence is undeniable.
If the result is false, the transaction is invalid and the computer rejects it. This can have different reasons. For example, the signature may not match the public key, which means someone other than the owner may have tried to send the bitcoin. Or the transaction may have been modified during transmission, which caused the fingerprint to change.
Beyond the signature, the computer also confirms that Alice has the bitcoin she wants to send and that she has not already spent it in another transaction. There are additional checks, but they are outside the scope of this series.
Once the transaction is verified, the computer forwards it to other computers in the network, where it is verified again. Within seconds, the transaction spreads across the globe.
Contents of a Transaction
We now know how a transaction is secured. But what does it actually contain? The following is a simplified view. The actual structure of a Bitcoin transaction is more complex, but these are the essential elements.
The hash of a transaction serves as its unique identifier. A transaction contains:
- the amount of bitcoin to be transferred from sender (Alice) to receiver (Bob
- the address of the receiver
- the signature, created by the sender
- the public key of the sender
Now that we know what a transaction is and how it is secured, the next question is: how are transactions permanently recorded?
What Is a Block?
After transactions are verified, they wait to be included in a block. Special computers in the network, called miners, each independently collect verified transactions and assemble them into a new block. A block is a container that holds a set of these verified transactions together with a block header.
Like a transaction, a block can also be identified by a unique hash. More specifically, this hash is computed from the block header, which is why it is called the block header hash.
But what does the header contain? Let's go through its components. As before, this is a simplified view.
Contents of the Block Header
Merkle Root
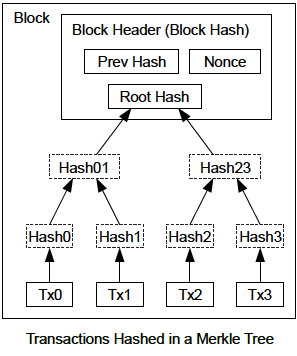
The header contains a single hash that represents all transactions in the block. This hash is called the Merkle Root, and it is built from the bottom up, like a pyramid.
The transactions form the base. Each transaction is hashed individually. Then, two neighboring hashes are combined and hashed together, forming the next layer. Those results are paired and hashed again, layer by layer, until a single hash remains at the top: the Merkle Root. This means any change to any transaction in the block is reflected in a single hash in the header.
Previous Block Hash
The header also contains the hash of the previous block. This is what connects blocks to each other. Each block points back to the one before it, forming a chain. This is where the name "blockchain" comes from. I will explain what this chain looks like in the next section.
Timestamp
A timestamp records when the block was created.
Mining Parameters
Finally, the header contains parameters related to the mining process. Mining is the mechanism that determines which computer gets to add the next block to the chain. I will explain how this works in the next article.
Now that we know what a block is and what it contains, the last question remains: what happens when blocks are linked together?
What Is the Blockchain?
As we have just seen, each block stores a reference to the one before it. What happens when you connect blocks this way, one after another?
The result is a chain of blocks: the blockchain. It is an ordered, backward-linked sequence of blocks. Each block points back to the one before it through its previous block hash, but not forward. The chain is built from the past toward the present. Together, the blocks form a complete history of all confirmed transactions, from the Genesis Block until now.
This structure has a powerful consequence. What happens if someone tries to change a transaction in an old block? That single change sets off a chain reaction. The modified transaction produces a different hash. This changes the Merkle Root, which changes the block's hash. But the next block has the original hash stored in its header. It no longer matches. To fix that, the attacker would have to change the next block too. But that changes its hash, which breaks the block after that, and so on. A single changed transaction breaks every block that follows. The deeper a block is buried in the chain, the more blocks would need to be recalculated.
This makes the blockchain tamper-evident: any manipulation becomes visible as soon as the hashes are verified, which happens automatically whenever a computer in the network receives a block. But being able to detect tampering is not the same as being able to prevent it. What actually prevents someone from recalculating the entire chain? The answer lies in the consensus mechanism and the mining process, which I will explain in the next article. They add a second layer of protection that makes the blockchain not just tamper-evident but tamper-resistant, and in practice, effectively immutable.
Conclusion
A transaction is created and signed by the sender, then verified by the network. The signature proves authenticity, integrity, and non-repudiation. The transaction is then included in a block and added to the blockchain, where the chain of hashes makes the entire history tamper-evident.
In the next article, I will explain what prevents attackers from recalculating the chain: a decentralized network and a consensus mechanism called Proof-of-Work.
If you have questions or feedback, feel free to reach out. And if you found this article helpful, consider sharing it with others who want to understand Bitcoin.



